Home »
DBMS
Lock-Based Protocol in DBMS
DBMS | Lock-Based Protocol: In this tutorial, we will learn about the lock-based protocol and types of lock-based protocols in the Database Management System.
By Pratishtha Saxena Last updated : May 31, 2023
What are Locks in DBMS?
In database management systems (DBMS), locks are mechanisms used to control concurrent access to shared resources, such as database tables, rows, or other objects. Locks help ensure data integrity and prevent conflicts that can arise when multiple transactions try to access or modify the same data simultaneously.
What are Lock-Based Protocol in DBMS?
Lock-based protocols are concurrency control mechanisms used in database management systems (DBMS) to coordinate the access and modification of shared resources, such as database objects or records, among concurrent transactions. These protocols use locks to enforce serializability and ensure data integrity in a multi-user environment.
Types of Locks in DBMS
DBMS typically supports two types of locks:
1. Shared Lock (Read Lock)
- Shared locks, also known as read locks, allow multiple transactions to concurrently read a shared resource without interfering with each other.
- Transactions acquiring a shared lock can read the data but cannot modify it.
- Shared locks are compatible with other shared locks, allowing multiple transactions to hold shared locks simultaneously.
- Shared locks promote concurrency by allowing concurrent read operations but restrict write operations until all shared locks are released.
2. Exclusive Lock (Write Lock)
- Exclusive locks, also known as write locks, grant exclusive access to a resource for a single transaction, preventing other transactions from simultaneously reading or modifying the same resource.
- Transactions acquiring an exclusive lock have both read and write privileges on the resource.
- Exclusive locks are not compatible with any other lock, including shared locks or other exclusive locks.
- Exclusive locks ensure data consistency by preventing conflicts caused by simultaneous modifications to a resource.
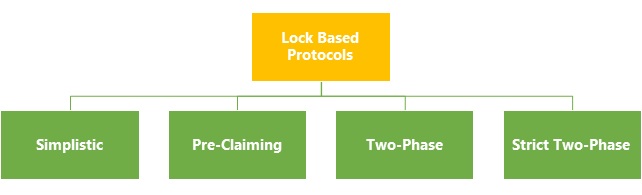
Types of Lock-Based Protocols in DBMS
There are several types of lock-based protocols used in database management systems (DBMS) to control concurrency and ensure data consistency among concurrent transactions. Some commonly used lock-based protocols are simplistic lock protocol, pre-claiming lock protocol, two-phase locking protocol, and strict two-phase locking protocol. Let us discuss them in detail.
1. Simplistic Lock Protocol
It refers to a simplified or basic approach to lock-based protocols. In a simplistic lock protocol, the emphasis is on simplicity and ease of implementation rather than sophisticated concurrency control mechanisms.
Here, transactions acquire locks on individual data objects before performing write operations on them. Once the write operation is successfully executed, the transaction can release the lock on the respective data item.
2. Pre-claiming Lock Protocol
In a pre-claiming lock protocol, a transaction analyses the data items it needs to access or modify and requests all the necessary locks from the database management system (DBMS) before it begins its execution. The protocol ensures that the transaction obtains all the required locks upfront.
The pre-claiming lock protocol aims to minimize the delays caused by lock acquisition during transaction execution. Obtaining all the required locks upfront, reduces the likelihood of conflicts and locks contention during the transaction's execution phase.
3. Two-Phase Locking Protocol
Two-Phase Locking is a well-known protocol that divides the lock-based execution of a transaction into two phases: the growing phase and the shrinking phase.
In the growing phase, a transaction acquires locks and does not release any locks until it reaches a point where it starts releasing locks in the shrinking phase.
The protocol ensures strict serializability by preventing conflicts between transactions, as no transaction can acquire a lock after releasing any lock.
4. Strict Two-Phase Locking Protocol
Strict Two-Phase Locking is an extension of the Two-Phase Locking protocol that enforces stricter rules regarding lock release.
Under Strict 2PL, a transaction holds all its locks until it commits or aborts, meaning no locks are released during the transaction's execution.
This protocol guarantees strict serializability, but it may result in longer lock-holding times, potentially impacting concurrency.
Conclusion
Hence, these lock-based protocols provide different trade-offs between concurrency and data consistency, allowing DBMS to manage concurrent access to shared resources effectively. The choice of protocol depends on factors such as the application requirements, expected transaction workload, and the desired level of concurrency and data consistency guarantees.
Advertisement
Advertisement