Home »
Computer Network
Aloha: A random access method of multiple access in Computer Network
In this tutorial, we will learn about a random access method known of multiple access that is ALOHA.
By Radib Kar Last updated : May 05, 2023
Aloha
In the earlier discussion, we saw that random access methods are one kind of multiple access protocols. Aloha is one of the random access methods that was introduced in the early 70's. It was designed for radio (wireless) LAN, but it can be used on any shared medium.
Types of Aloha
Aloha is basically of two types,
- Pure Aloha
- Slotted Aloha
We are going to see about both in details here.
1. Pure Aloha
The original ALOHA protocol is called pure ALOHA. The idea behind the protocol is that each station sends a frame whenever it has a frame to send. However, since there is only one channel to share, there is the possibility of collision between frames from different stations. Figure 1 shows an example of frame collisions in pure ALOHA.
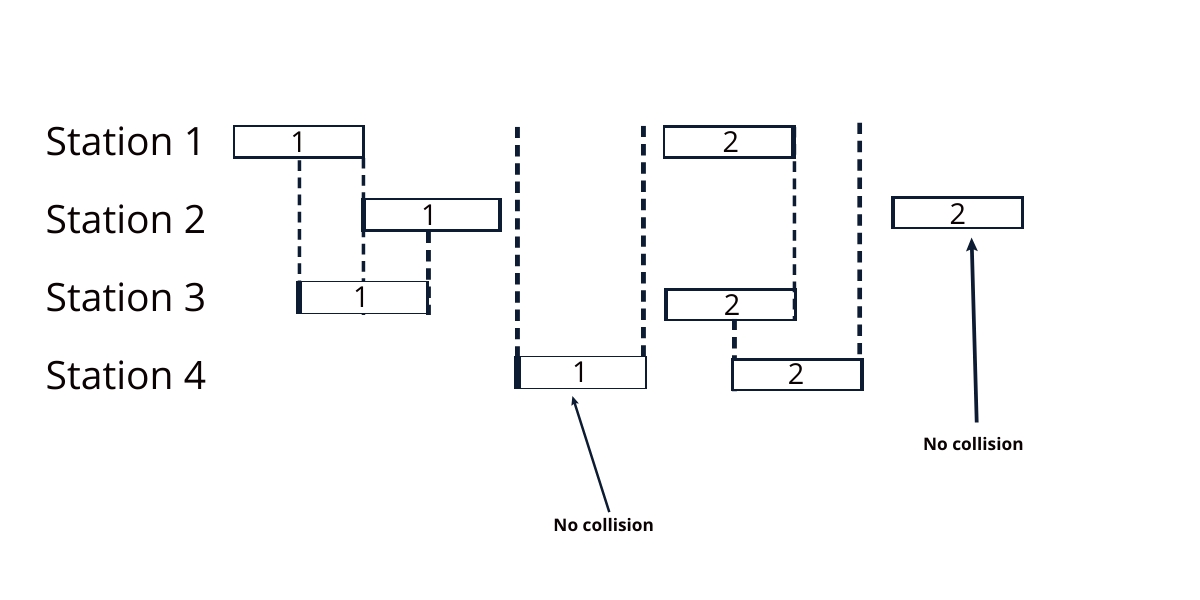
Figure 1: collisions
So, there are four stations in the above figure that contend with one another for access to the shared channel. The figure shows that each station sends two frames; there are a total of eight frames on the shared medium. Some of these frames collide because multiple frames are in contention for the shared channel.
Only two frames survive which are frame2 of station2 and frame1 of station4. But others are lost due to the collision. Thus the stations need to resend those collided frames. But how the sender is confirmed that the sent frame is lost? It's the acknowledgment frame sent by the receiver. The sender waits for the acknowledgment frame from the receiver. If it doesn't receive the acknowledgment frame before time-out then it resends.
Here the Aloha protocol comes in action. If all the sender sends the lost frames again together then there can be collisions again. Hence, aloha protocol says that the senders wait for a random amount of time. This randomness helps to avoid further collisions. We call this back-off time. Let's understand the protocol.
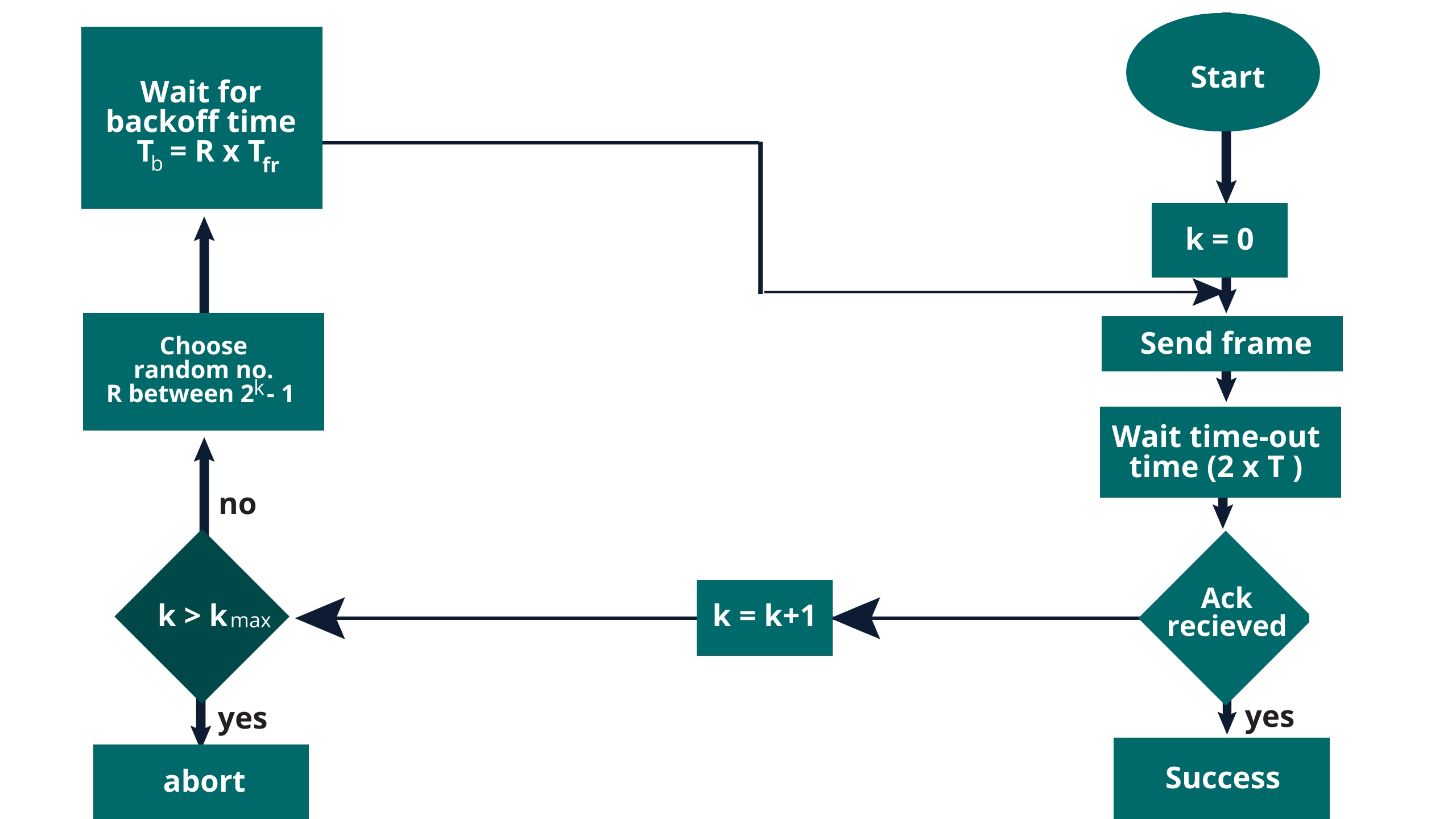
Figure 2: Aloha protocol
Tp = propagation time
Tb = back-off time
Tfr = frame transmission time
Kmax = 15 normally
Pure ALOHA vulnerable time = 2 x Tfr
Throughput:
S = G*e-2G
G = no. of average frames generated in Tfr
Maximum throughput is 0.184 when G=1/2
2. Slotted Aloha
Slotted Aloha is a modified version of pure aloha where we divide the time into slots of Tfr. Thus, If a station fails to send the frame in one slot it can't send throughout that slot and have to wait for the next slot beginning. This successfully reduces the vulnerable time down to Tfr which was previously 2* Tfr for pure aloha. Throughput also increases and turns to be G*e-G, where max throughput becomes .368 when G=1
Advertisement
Advertisement