Home »
Cloud Computing
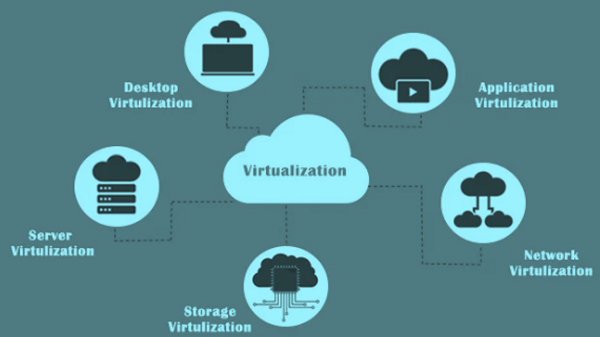
Types of Virtualization in Cloud Computing
Cloud Computing | Virtualization Types: In this tutorial, we will learn about the various types of virtualizations in the cloud computing environment.
By IncludeHelp Last updated : June 02, 2023
The following are the types of virtualization in Cloud Computing:
1) Virtualization at a server
Physical servers are the platform for files and software, such applications are stored on the server computer and can be accessed via a network. This approach to server multicore processing means each physical server normally runs a single unique application at a time. They may be able to use a little online when they are not busy, but in general, they can only use a fraction of their hardware.
The function of virtualization techniques, including server virtualization, is that it is used to turn a server into multiple virtual machines. These virtual machines all use the server's resources and will operate as physical devices independent of one another, allowing us to delegate the server's computing capabilities as we see fit.
2) Virtualization of hardware
Hardware virtualization is the process of using software to simulate a device. When the VMM or VM software is directly mounted on the hardware system is known as hardware virtualization.
3) Virtualization applied to data
In this abstraction of technical details of the on-site and off-site data, the companies get the ability to scale their IT cloud storage and virtualization needs, at the same time the company gets the ability to do whatever IT support they need without having to think about the details of IT management.
4) Application virtualization
Running an application once in the beginning uses the current operating system and its hardware resources. We are running the machine as an application, basically to our needs. Application virtualization is, among other things, securing the application and the operating system from each other. Often the software will allow us access to it without the app is loaded into the native computer.
Due to virtualization, the administrator cans virtualize the program in a semi-virtual environment. Any form of a user who has access to the server would be able to access the application and run it as if it were virtualized on their respective computer. The application itself is not virtualized in any devices. These applications allow us to run it on a portable computer, such as a tablet or phone, and then when we move to a new device we can continue using the program.
5) Network Virtualization
Comparing this to the "cloud" (Network Virtualization in cloud computing is a way of integrating the available resources in a network by breaking up the available bandwidth into various networks, each being distinct and differentiated) Like Windows have a "group" setting and Mac has an "individual" setting, e-cigarettes can also be put into individual and group categories. The idea is that the technology disguises the true complexity of the network by splitting it into sections that are easy to handle, just as our segmented hard drive makes it easier for us to manage data.
6) Operating system Virtualization
When the virtual machine programme or virtual machine manager (VMM) is mounted on the Host operating system instead of directly on the hardware system is known as operating system virtualization.
7) Desktop virtualization
Desktop virtualization is a method whereby one can build a virtual desktop of their actual desktop's desktop and migrate it to a remote data center for troubleshooting purposes. Though it sounds complicated, it is not any different than remote accessing a device from a mobile phone, though we tend to use a thin client to access it.
8) Data Storage virtualization
Storage virtualization involves taking all the physical storage devices and abstracting i.e. logically organizing them into a single store located in a lab. Then it can be centrally controlled from a server or any other computer. When the balance protecting card will be filled it will seem like there is only one storage unit.
Advertisement
Advertisement