Home »
Cryptography
Output Feedback Mode (OFB) in Cryptography
Cryptography | Output Feedback Mode (OFB): In this tutorial, we will learn about the output feedback mode, its operations, advantages, and disadvantages.
By Monika Sharma Last updated : May 25, 2023
Output Feedback Mode (OFB)
This is an output feedback (OFB) mode is similar in structure to that of CFB in Cryptography. It is the output of the encryption function that is fed back to the shift register in OFB in the cryptography, whereas in CFB in the mode of blocks, the ciphertext unit is fed back to the shift register in the block. The other difference is that the OFB mode operates on full blocks of plaintext or original text and ciphertext, not on an s-bit subset of character. Encryption can be expressed as,
Cj = Pj Ⓧ E(K, [Cj - i Ⓧ Pj - 1])
By manage the terms, we can demonstrate that decryption works as we like,
Pj = Cj Ⓧ E(K, [Cj - 1 Ⓧ Pj - 1])
Output Feedback Mode (OFB) Operations
- Let the size of a block of the character be b. If the last block of plaintext or original text contains u bits (indicated by *), with u 6 b, the most significant u bits of the last output block ON are used for the XOR operation; the remaining b -u bits of the last output block are discarded in the cryptography.
- Like as with CBC and CFB, the OFB mode requires an initialization vector in the system. In the case of OFB, the IV must be a nonce; that is, the IV must be unique to each execution of the encryption operation in the cryptography. The reason for this is that the sequence of encryption output blocks of the character, Oi, depends only on the key and the IV and does not depend on the plaintext or original text. Therefore, for a given key and IV, the stream of output bits used to XOR with the stream of plaintext or original text bits is fixed. If two different messages had an identical block of plaintext or original text in an identical position, then an attacker would be able to determine what portion of the Oi stream in the cryptography.
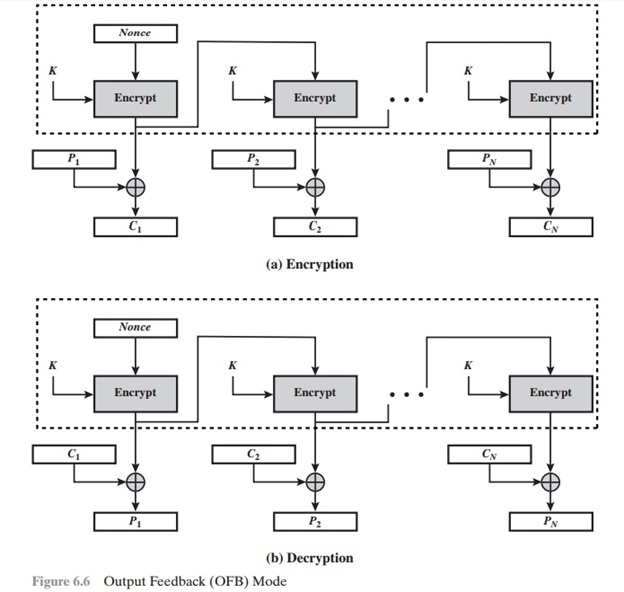
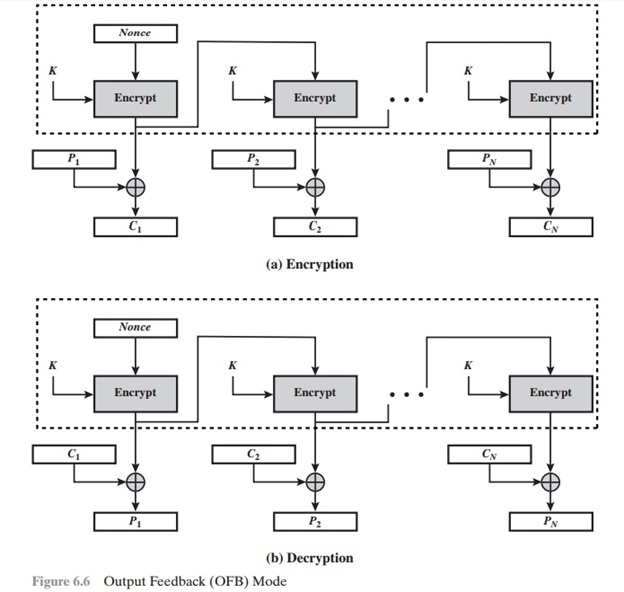
Image source: https://www.brainkart.com/article/Output-Feedback-Mode_8418/
Observe that complementing a bit in the ciphertext complements the corresponding bit in the recovered plaintext or original text. Thus, controlled changes to the recovered plaintext can be made. There was the mode of operation may make it possible for an opponent, by making the necessary changes to the checksum portion of the message as well as to the data portion, to alter the ciphertext as work with keys in such a way that it is not detected by an error-correcting code in the cryptography.
This is an OFB has the structure of a typical stream cipher, because the cipher generates a stream of bits as a function of initial value and a cryptography key, and that stream of bits is XORed with the plaintext bits or original text. The generated stream that is XORed with the plaintext or original text is itself independent of the plaintext or original text; this is highlighted by dashed boxes. One distinction from the stream ciphers is that OFB encrypts plaintext a full block at a time, where typically a block is 64 or 128 bits of the character. Many stream ciphers encrypt one byte at a time in this mode of operation.
Output Feedback Mode (OFB) Advantages
- The main advantage of the OFB method is that bit errors in transmission do not propagate in the encryption.
- For example, if as a bit error occurs in C1 as ciphertext, only the recovered value of P1 as plaintext is affected; subsequent plaintext units are not corrupted. With CFB, C1 as ciphertext also serves as input to the shift register and therefore causes additional corruption downstream in this mode.
Output Feedback Mode (OFB) Disadvantages
- The disadvantage of OFB is that it is more vulnerable to a message stream modification attack than is CFB in the modes of operation.
Advertisement
Advertisement